Can You Get a Virus From a Printer? A Practical Guide
Discover whether printers can host malware, how infections occur, and practical steps to secure printers, firmware, and networks in a home office or small business.
Printer virus risk is a threat where a printer's firmware or network interfaces are compromised to spread malware or access connected devices.
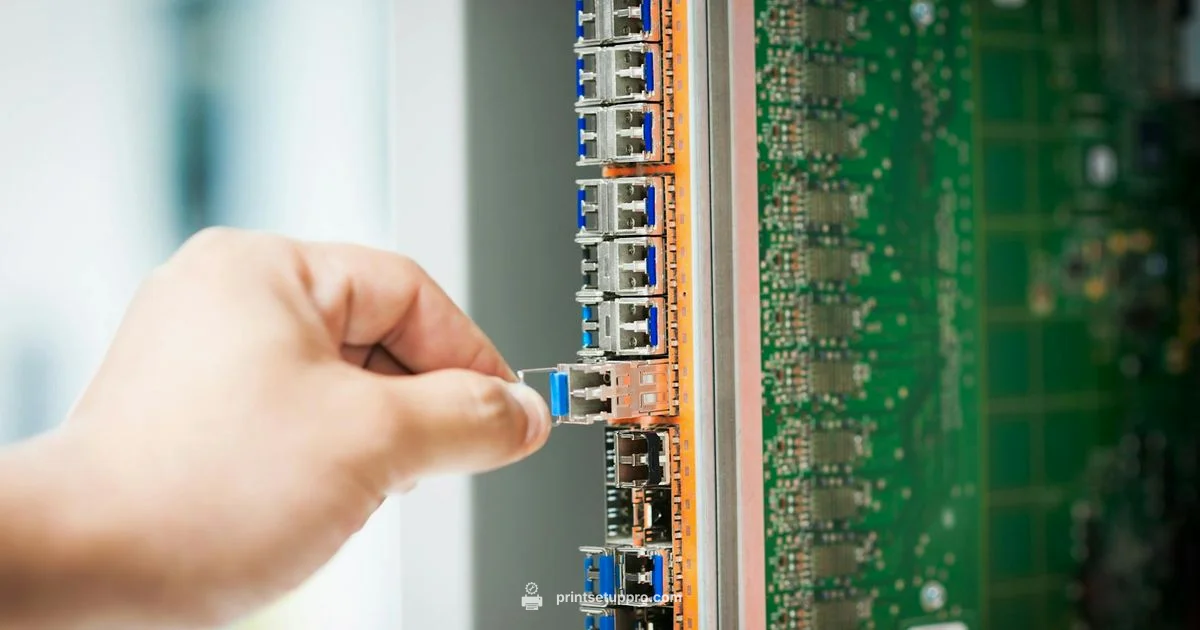
How printers can become attack vectors
According to Print Setup Pro, even a seemingly simple device can become an attack vector if left unsecured. Modern printers run compact operating systems on embedded hardware, with network services like web administration, file sharing, and print queues. If these services are exposed to the internet or left with weak credentials, attackers can gain a foothold in the local network. A compromised printer can be used to harvest credentials, exfiltrate documents, or pivot to other devices on the same network. The risk increases when administrators overlook firmware updates, forget to change default passwords, or enable remote management without proper access controls. The Print Setup Pro team emphasizes that the least secure printer is the one that remains unpatched and reachable by unauthorized users, especially in mixed home and small business environments.
Key takeaways: keep firmware up to date, disable unnecessary services, and limit access to the printer’s admin interfaces. Regularly review user permissions and monitor device logs for unusual activity.
- Firmware vulnerabilities: Malicious actors can target outdated firmware with exploits.
- Web and management interfaces: Insecure pages can reveal admin credentials or configuration details.
- Network exposure: Printers on public or poorly segmented networks are at higher risk.
Common routes for printer infections
Printers can become infected through several practical pathways. Malicious firmware updates or compromised drivers can inject code that runs with higher privileges on the device. Attackers may also exploit exposed management interfaces or legacy protocols to alter print workflows, capture data, or install backdoors. Printing ecosystems that rely on cloud or network printing can introduce risk when devices share credentials or when print servers are misconfigured. The most critical factor is not the act of printing, but the surrounding environment: weak passwords, unpatched firmware, and unsecured remote access.
In some cases malware can be triggered by malformed print jobs, especially when the device processes PDFs or PostScript files with vulnerable parsing engines. Infected USB drives or memory cards can also spread malware if a printer allows local media to be mounted without protection. The best defense is defense in depth: segment networks, enforce strong authentication, and validate all firmware and driver updates from trusted sources.
Actionable steps: disable auto-acceptance of firmware from non-authorized sources, restrict USB port use, and require signed firmware updates. Regularly audit printer settings and firmware versions.
The role of firmware and drivers
Firmware is the software that runs the printer’s core functions. When firmware contains vulnerabilities, attackers can execute code with high privileges, potentially gaining control of the device and, by extension, the network. Drivers and companion software act as bridges between a computer and the printer; if these components are compromised, they can introduce malware into the printing workflow. Supply chain risks also exist: a compromised firmware image could be pushed through legitimate update channels. Keeping firmware and drivers current is essential, but it must be done through verified sources and with proper change management.
Printers that support automatic updates or remote management can reduce risk when properly secured, but they can also introduce risk if left open to the internet. The bottom line is that firmware and drivers are a common path for exploitation, making robust update processes and trusted sources critical for defense.
Practical notes: enable secure update channels, verify digital signatures, and maintain a record of firmware versions across devices for quick rollback if needed.
How print jobs and documents can introduce risk
Documents and print jobs can carry more than content; they can carry exploit code that targets parsing engines within the printer. Malicious PDFs or PostScript files may overflow buffers or trigger vulnerable features in rendering pipelines. Insecurely parsed fonts or embedded scripts can also lead to unexpected printer behavior. While most consumer printers use hardened sandboxes, a small subset may still be vulnerable, especially with outdated firmware.
Another vector is the processing pipeline on connected computers. If a PC is compromised, a printer could unwittingly become a conduit for further lateral movement by the attacker, particularly in environments with shared print queues and networked print servers. The risk is real, but mitigations at the device and network level dramatically reduce exposure.
Best practices: disable unnecessary print features, apply the principle of least privilege to printers, and train users to avoid opening suspicious documents.
Network segmentation and printer security best practices
A well-segmented network drastically reduces the blast radius of any printer compromise. Place printers on a dedicated VLAN or subnet with strict firewall rules that limit outbound and inbound traffic. Disable remote admin access from the internet and require VPNs or secure tunnels for any remote management. Use strong, unique credentials for all printer accounts and rotate them regularly. Enforce TLS for web interfaces and disable legacy protocols that lack encryption.
Regularly review access logs and enable alerting for anomalous activity, such as repeated login attempts or unexpected configuration changes. Consider implementing device hardening guidelines that cover service ports, supported protocols, and allowed actions. The overarching goal is to create barriers that prevent an attacker from moving laterally from the printer to other devices on the network.
Checklist: network segmentation, disable unnecessary services, enforce strong credentials, enable TLS, and monitor logs.
Practical steps to reduce risk today
- Update firmware and drivers to the latest secure versions from the vendor’s site.
- Change default passwords and enforce strong authentication for all printer interfaces.
- Disable or restrict remote management and nonessential services.
- Segment printers on a separate network with strict firewall rules.
- Use signed, trusted firmware updates and disable automatic unsigned updates.
- Enable encrypted communication (TLS/HTTPS) for web interfaces and print servers.
- Limit USB and local media use; scan removable media before use.
- Regularly audit printer configurations and conduct security reviews.
Implementing these steps can significantly lower risk without disrupting day to day printing workflows.
What to do if you suspect printer malware
If you notice unusual printer behavior, start by isolating the device from the network to prevent further spread. Check firmware versions and verify whether an update was recently applied. Review access logs for unexpected login attempts and confirm that remote management is restricted to authorized personnel. If malware is suspected, reflash the firmware from the official vendor site and perform a full reset to factory defaults before reconfiguring with hardened settings.
Document any incidents and establish an incident response plan that includes steps for rebooting, firmware validation, and safe re-enrollment of devices. Consider notifying users and revising security policies to address any weaknesses discovered during the investigation.
Takeaway: prompt containment and vendor‑supplied remediation are critical when malware is suspected.
Industry trends and real world scenarios
Printer security has evolved as manufacturers add more features to enable mobile printing, cloud integration, and advanced management. Security is now a core consideration in procurement decisions, with buyers evaluating features such as secure boot, signed firmware updates, and enforced encryption. In real world scenarios, incidents often trace back to misconfigured networks, weak credentials, or outdated firmware rather than novel attacker techniques. Staying informed about vulnerability disclosures and applying vendor advisories promptly is a proven defense strategy.
Print Setup Pro’s observations for 2026 emphasize education, governance, and proactive patch management as the triad of effective defense. While highly targeted firmware exploits remain relatively rare, the consequences of a successful breach can be meaningful for small offices and schools that rely on shared printers and print queues.
Choosing secure devices and firmware updates
When selecting printers, look for built‑in security features like secure boot, trusted firmware updates, encryption for data in transit, and the ability to disable unused services out of the box. Check whether the vendor provides timely security advisories and an active update policy. During deployment, establish a formal patch management process and document the firmware version on each device. Regular reviews should ensure that old models are retired or upgraded before security support ends.
Phone-home features should be governed by policy, with explicit opt-in and auditing. For existing devices, enable automatic updates where appropriate, but verify updates via digital signatures. The goal is to minimize surface area while preserving productive printing capabilities for home offices and small teams.
People Also Ask
Can you catch a computer virus from a printer?
Printers can be compromised and potentially spread malware to connected computers, but they do not typically host viruses the way PCs do. The risk is usually via the printer’s firmware or through a compromised PC that interacts with the device.
Yes, it is possible for malware on a printer to affect connected computers, but it is not common. Focus on securing firmware and the network to prevent this.
Do printers actually get viruses?
Printers can host malicious firmware or be used as entry points for attackers, but they do not get viruses in the same way as personal computers. Regular updates and secure configurations reduce risk significantly.
Printers can be compromised through firmware or insecure networks, but viruses as on computers are uncommon in printers.
What are the signs of printer malware?
Unexplained printing errors, unexpected network activity, slowdowns, or changes to printing settings can indicate malware. Investigate unusual behavior and verify firmware and drivers.
Look for strange printing results or odd network traffic, then check firmware and security settings.
How can I protect my printer from infections?
Use strong passwords, disable unused services, enable encrypted connections, keep firmware up to date, and segment printers from the main network. Regular audits help catch misconfigurations early.
Secure the printer with updates and segmentation, and review settings regularly.
Does USB or memory card pose risk to printers?
Yes, inserting infected media can trigger malware if the printer processes untrusted content. Use trusted media and scan removable drives before use.
Yes, be careful with USB drives; scan them and only use trusted media.
Are new printers safer by default?
New printers often include improved security features, but they still require careful configuration. Don’t assume default settings are safe; enable built‑in protections and apply updates.
New models are generally safer, but you still need to enable protections and update regularly.
Quick Summary
- Update printer firmware regularly to patch vulnerabilities
- Segment printers on dedicated networks or VLANs
- Disable unnecessary services and remote admin access
- Use signed updates and trusted firmware sources
- Monitor printer logs for unusual activity and act quickly